Malware Takedown Dismantles Major Malware Operations
Malware takedown efforts intensified this week as international law-enforcement agencies dismantled the infrastructure behind Rhadamanthys, VenomRAT, and Elysium. Authorities targeted large networks that controlled infected systems, harvested credentials, and enabled widespread cybercrime activity. Investigators coordinated across several countries and removed key servers, domains, and operational assets. This action delivers a significant blow to three prolific malware ecosystems. Scale of the

AsyncRAT Exploits ConnectWise in New Malware Campaign
AsyncRAT exploits ConnectWise in a recent malware campaign that highlights how attackers weaponize legitimate remote access tools. Security researchers uncovered a layered attack chain that delivered the trojan through fileless techniques, persistence tricks, and data theft. The operation reveals the growing sophistication of remote access trojans and the increasing risks for businesses relying on widely used IT management software. How

ToxicPanda Android Malware Infects Thousands Across Europe
A new wave of the ToxicPanda Android malware is sweeping through Europe, targeting mobile banking users with advanced theft and evasion tactics. First identified in 2022, this banking trojan has evolved into one of the most dangerous threats for Android users, using fake overlays and accessibility services to steal login credentials and bypass security. Recent reports show over 4,500 devices

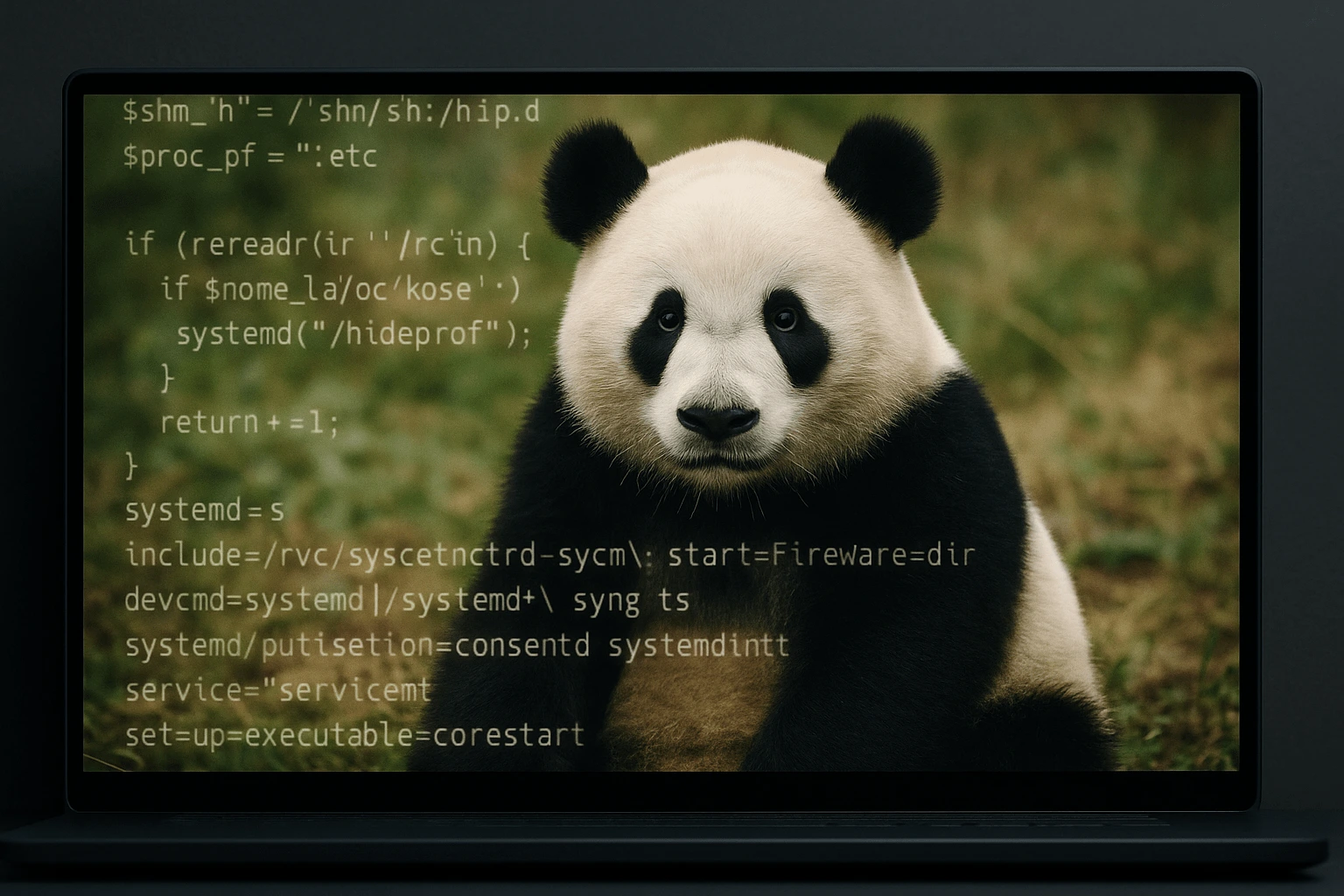
Koske Linux Malware Hides in Panda Images to Evade Detection
A new Linux malware named Koske is using panda-themed image files to hide its malicious payloads. The threat actors behind it are leveraging polyglot files, legitimate JPEGs with hidden executable code. This stealthy malware targets poorly secured JupyterLab servers to gain access and then installs rootkits and cryptocurrency miners. Security researchers at Aqua Security discovered the campaign and say Koske
Endgame Gear Malware Tool Infects Users Through Official Site
The official website of gaming mouse maker Endgame Gear recently hosted a malware-infected configuration tool, and it stayed live for over two weeks before anyone noticed. From June 26 to July 9, users downloading the setup tool for the OP1w 4K V2 mouse were unknowingly installing the XRed remote access trojan (RAT). The compromised version was distributed through Endgame Gear’s

Konfety Malware Uses Malformed APKs to Evade Android Detection
The Android threat landscape continues to evolve, and cybercriminals are now exploiting even the ZIP format’s underbelly. A newly discovered malware variant named Konfety is setting a dangerous precedent by manipulating how Android Package (APK) files are structured. This manipulation allows it to sidestep traditional analysis and detection methods used by antivirus programs, app stores, and researchers. What makes Konfety

LameHug Malware Uses LLM to Automate Windows Data Theft
LameHug, a newly discovered Python-based malware, is raising alarms in the cybersecurity world by becoming the first known malicious tool to leverage a large language model (LLM) in real time. This cutting-edge threat utilizes Hugging Face’s Qwen 2.5‑Coder‑32B‑Instruct model to dynamically craft Windows commands used for data theft and system reconnaissance, making detection and mitigation significantly more challenging. A New

Fake AI Gaming Firms Target Crypto Users with Malware Scam
Cybercriminals are using fake AI and gaming firms to trick cryptocurrency users into installing malware. These fake companies use professional websites, social media presence, and direct outreach to convince victims to download what they claim is "beta software". But it's actually malware designed to steal wallet credentials and other sensitive data. The campaign, active since early 2024 and still growing,

IconAds, a Massive Mobile Ad-Fraud Operation Disrupted
A sophisticated mobile ad-fraud operation, named "IconAds," has been disrupted. The dismantling came after it was discovered that 352 Android applications were secretly bombarding users with intrusive ads while hiding their presence on devices. This extensive campaign, which peaked at over 1.2 billion ad bid requests daily, primarily targeted users in Brazil, Mexico, and the United States. How the IconAds
Fake Zoom Campaign Steals Your Credentials: What To Do?
In a troubling new cybercrime campaign, hackers are deploying fake versions of the popular Zoom video conferencing app to steal sensitive personal data — including login credentials and cryptocurrency wallets. This scheme marks yet another evolution in phishing tactics, with attackers mimicking trusted software to target unsuspecting users. A Familiar App With a Dangerous Twist Security researchers have discovered several
