WordPress Theme Hijacked by Malware: What You Need to Know
A popular WordPress themes got hijacked by malware. A critical security flaw in one of the most widely used premium WordPress themes has put thousands of websites at risk. The Motors theme, developed by StylemixThemes and commonly used for car dealership and classified sites, has been found vulnerable to a serious exploit. Cybercriminals now actively use this exploit to hijack

Godfather Malware Is Coming for Your Banking Apps
A new wave of Android-targeting malware is sweeping across devices, and this one is after your money. Called Godfather malware, this powerful banking trojan disguises itself as legitimate apps while quietly hijacking your personal data, banking credentials, and even bypassing two-factor authentication. What Is Godfather Malware? Godfather is an Android banking trojan designed to steal login credentials by impersonating over

BADBOX 2.0: How Your TV Could Be a Botnet Node
Imagine buying a brand-new smart TV or streaming box, still sealed in its packaging. Only to find out later that it was already compromised by hackers before it ever reached your hands. That’s the chilling reality behind BADBOX 2.0, a global botnet campaign that has turned over a million consumer devices into unwitting cyber weapons. The FBI is sounding the

Chaos RAT Malware Targets Windows and Linux
.ProvideA new wave of cyberattacks is leveraging an evolved version of Chaos RAT malware, an open-source remote access trojan that now poses a significant threat to both Windows and Linux systems. By disguising itself as a legitimate network utility, this malware is quietly infiltrating machines and granting attackers extensive control over compromised devices. What Is Chaos RAT Malware? Chaos RAT

Crocodilus Malware Adds Fake Contacts to Your Android Phone
The newly discovered Crocodilus malware raises serious concern among cybersecurity experts. Unlike typical trojans, this malware introduces a deceptive twist: it secretly adds fake contacts to your phone to impersonate trusted names like banks, family members, or service providers. This manipulation makes phishing attempts feel far more convincing, and far more dangerous. Here's what you need to know about how

AyySSHush Botnet Hacks ASUS Routers to Add SSH Backdoor
The newly discovered AyySSHush botnet campaign has silently compromised over 9,000 ASUS routers, installing a persistent SSH backdoor using a series of sophisticated and stealthy techniques. The campaign highlights a growing threat to home and small office routers, leveraging legitimate features to maintain control, all without deploying traditional malware. Security researchers at GreyNoise uncovered the campaign in mid-March 2025, but

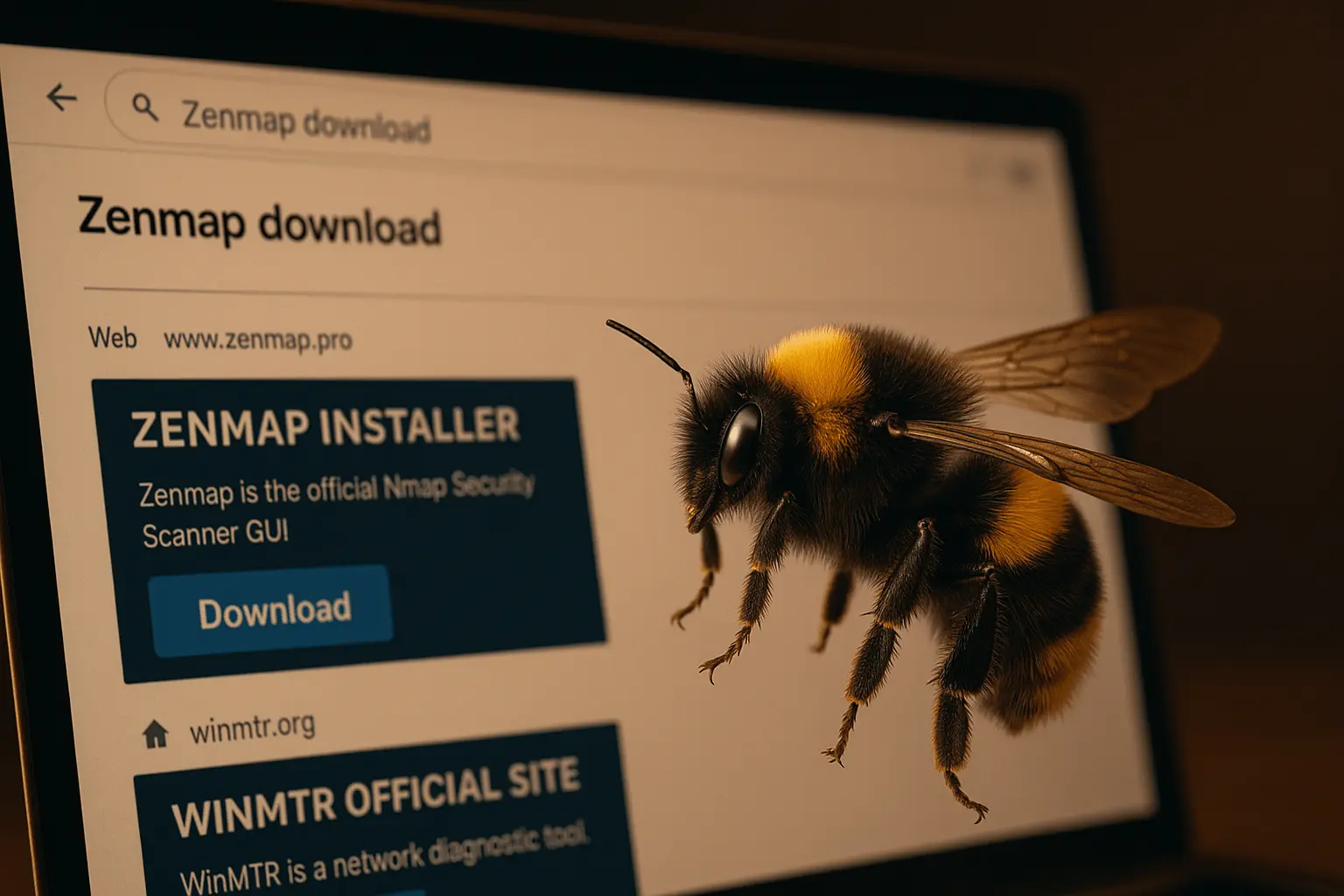
Bumblebee Malware Returns with SEO Poisoning Campaign
Bumblebee malware has re-emerged with a clever and concerning new distribution method. Threat actors are now using search engine optimization (SEO) poisoning to push trojanized versions of trusted networking tools like Zenmap and WinMTR, successfully deceiving even tech-savvy users into downloading malicious software. This campaign underscores the growing sophistication of cyber threats and the need for constant vigilance. What Is
TikTok Videos Spread Malware via ClickFix Attacks
TikTok, the go-to platform for viral dances, life hacks, and bite-sized entertainment, has now entered the radar of cybersecurity experts for a far more sinister reason. A recent report from Trend Micro reveals that cybercriminals are using TikTok videos to spread infostealer malware in a new and deceptive tactic known as "ClickFix." What Is ClickFix? ClickFix is a social engineering

Malicious Chrome Extensions Are Stealing Your Data
In a new and alarming cybersecurity report, over 100 malicious Google Chrome extensions have been discovered impersonating trusted tools like Fortinet VPN, YouTube downloaders, and AI services. These deceptive extensions were designed not only to lure users with familiar branding, but also to steal sensitive browser data and inject remote scripts. This poses a major threat to anyone using the

Lumma Stealer Disrupted After Infecting 10 Million Devices
In a major win for global cybersecurity, a widespread malware campaign known as Lumma Stealer (LummaC2) has been successfully disrupted after compromising an estimated 10 million systems worldwide. This malicious software, designed to harvest sensitive personal and financial data, had quickly become a tool of choice for cybercriminals across the globe. The takedown marks one of the most significant actions
