MuddyWater False Flag Attack Hid Behind Chaos Ransomware
What looked like a ransomware attack earlier this year turned out to be something far more calculated. Security researchers have linked a sophisticated intrusion to MuddyWater, an Iranian state-sponsored hacking group, in what has been assessed as a deliberate false flag attack designed to look like the work of a criminal ransomware gang. The Chaos Ransomware Cover Story Chaos is

Trigona Ransomware Returns With Custom Data Theft Tool
Trigona ransomware is back, and it has upgraded its playbook. New attacks observed in March 2026 show the group using a purpose-built data theft tool — one designed specifically to fly under the radar of modern security software. The shift marks one of the more technically significant developments in the ransomware landscape this year, and it raises a serious question:

Kyber Ransomware Hits Windows and VMware With PQC Twist
A new cyber threat is making waves in the security community — and it comes with a bold claim. Kyber ransomware has emerged as a cross-platform operation hitting both Windows file servers and VMware ESXi infrastructure, with operators advertising post-quantum encryption as part of their attack. The reality, however, is more complicated than the ransom note suggests. Two Variants, One

Advantest Ransomware Attack Disrupts Chip Supply Chain
Advantest ransomware attack news has raised fresh concerns across the semiconductor sector after the Japanese technology giant confirmed a cyber intrusion into its corporate network. The company detected suspicious activity on February 15 and immediately activated its incident response protocols to contain the threat and protect critical systems. Advantest later confirmed that attackers gained unauthorized access and deployed ransomware on

RansomHouse Encryption Upgrade Complicates Recovery
Ransomware groups continue to refine their tools, and the latest RansomHouse encryption upgrade shows how quickly these threats evolve. Security researchers have identified a new encryptor used by the group that applies multi-layered data processing, making file recovery significantly harder after an attack. Instead of relying on a single encryption pass, the updated ransomware processes data in multiple stages. Each

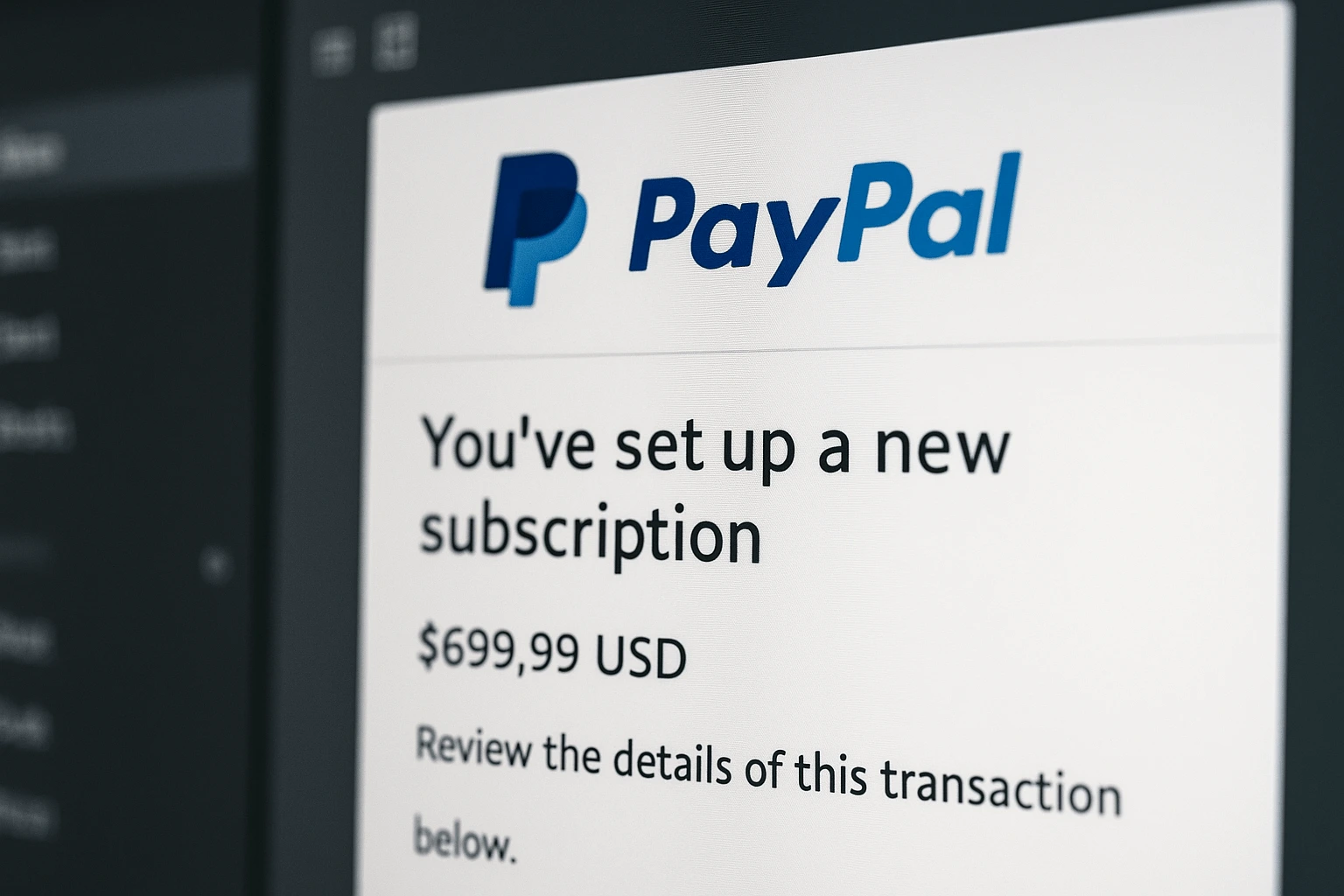
PayPal Subscription Scam Abuses Legitimate Billing Emails
A PayPal subscription scam is circulating that does not rely on fake domains, malicious links, or compromised accounts. Instead, it abuses a legitimate PayPal feature to deliver fraudulent messages directly from PayPal’s own email infrastructure. The result is a scam that bypasses many traditional warning signs and places users at risk through trust rather than technical deception. Security researchers warn
CyberVolk Ransomware Trips Over Its Own Encryption
CyberVolk ransomware appeared suddenly and attempted to establish itself as a serious new extortion threat. Security researchers quickly discovered that the operation suffers from critical technical weaknesses. The most damaging issue involves broken cryptography that prevents the malware from securely encrypting victim data. A new ransomware group enters the scene CyberVolk ransomware surfaced as a previously unknown operation targeting Windows

DroidLock Android Malware Triggers Full Device Lockouts
Growing reports about DroidLock Android Malware reveal how fast mobile ransomware continues to evolve. The new strain targets users who install apps from untrusted sources and locks their devices with an aggressive screen overlay. Its behaviour shows a worrying shift toward full device takeover on Android systems. How DroidLock Infects Devices Attackers distribute DroidLock through malicious apps found outside official

Storm-0249 Ransomware Escalation Expands Global Attack Risks
Security teams face rising pressure as new intelligence confirms a clear Storm-0249 ransomware escalation. The threat group, long linked to espionage operations, now intensifies its focus on destructive and financially driven attacks. Microsoft reports that the actors increased their use of custom payloads and enhanced lateral-movement methods. This shift signals a broader strategy that blends intelligence collection with aggressive extortion.

Qilin Ransomware Is Behind the Asahi Brewery Attack
The Qilin ransomware group has officially claimed responsibility for the recent cyberattack on Japan’s Asahi Breweries, publishing proof-of-hack samples and boasting of a massive data theft. This development follows Asahi’s confirmation last week that a ransomware incident disrupted beer production across Japan. According to Qilin’s leak site, the group allegedly exfiltrated around 27GB of data from Asahi’s internal systems, including
