A PayPal subscription scam is circulating that does not rely on fake domains, malicious links, or compromised accounts. Instead, it abuses a legitimate PayPal feature to deliver fraudulent messages directly from PayPal’s own email infrastructure. The result is a scam that bypasses many traditional warning signs and places users at risk through trust rather than technical deception.
Security researchers warn that this tactic represents a growing trend in platform abuse, where built-in systems function correctly but are manipulated to achieve malicious outcomes. In this case, PayPal’s subscription notifications become the delivery mechanism for fake purchase alerts designed to trigger panic and hasty action.
How the scam operates inside PayPal’s system
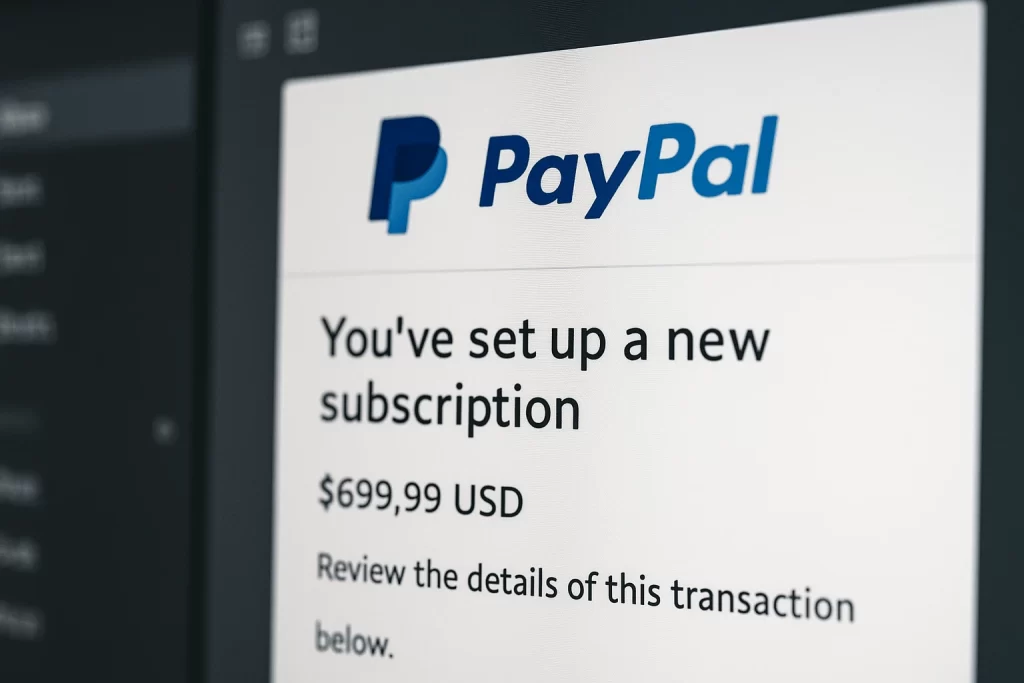
The scheme begins with attackers creating genuine PayPal subscriptions using their own accounts. During the setup process, PayPal allows merchants to customize fields such as subscription names and descriptive notes. Scammers exploit these fields by inserting alarming messages that resemble fraud alerts or billing disputes.
Once the subscription is created, PayPal automatically sends a notification email to the targeted user. That message is delivered from PayPal’s official domain and follows the platform’s standard billing format. From a technical perspective, the email is legitimate. From a security perspective, the content is deceptive.
This distinction makes the scam difficult to detect through automated filtering and harder for users to question instinctively.
Why the emails feel credible to recipients
PayPal billing emails already carry an inherent sense of urgency. Users associate them with real financial activity and potential loss. When a message claims a large charge or subscription payment, recipients often react emotionally before verifying details.
The scam avoids common phishing patterns. Most messages contain no links and no attachments. Instead, they include a phone number presented as PayPal customer support. This approach sidesteps many user education warnings that focus on suspicious links and fake login pages.
The trust placed in transactional emails becomes the attack surface.
The shift from email fraud to phone-based manipulation
Once a victim calls the number, the scam moves into a social engineering phase. Attackers impersonate PayPal support staff and reinforce the urgency created by the email. Victims may be told their account is compromised or that immediate action is required to stop further charges.
From there, attackers attempt to extract sensitive information, guide victims through fake refund processes, or persuade them to install remote access software. In more advanced cases, scammers aim for full account takeover or direct financial transfers under the guise of account recovery.
The email itself is only the entry point.
Why this abuse is difficult to prevent
PayPal’s subscription feature works as intended and supports legitimate businesses that rely on flexible billing communication. Restricting customization could disrupt real merchants and service providers. That creates a challenge for mitigation without harming normal platform use.
Transactional emails also receive preferential treatment across email systems, which further limits defensive options. As long as the platform sends the message, technical blocking remains complex.
PayPal’s guidance to users
PayPal has acknowledged reports of subscription email abuse and says it is reviewing the issue. The company advises users to avoid calling phone numbers included in billing emails and to verify activity directly through the PayPal account dashboard.
Unexpected subscriptions or charges should be reviewed inside the account interface, not through contact details provided in an email.
Final Thoughts
The PayPal subscription scam highlights a broader shift in online fraud toward exploiting trust rather than exploiting vulnerabilities. No systems are breached, and no malware is deployed. Instead, attackers weaponize legitimate features to reach users where skepticism is lowest.
As platforms continue expanding automated notifications and flexible messaging tools, this type of abuse is likely to grow. For users, careful verification remains the most reliable defense when even legitimate emails can be part of a scam.