SystemBC Malware Turns VPS Into Proxy Networks
SystemBC malware is evolving into a powerful tool for cybercriminals. First spotted in 2019, it has shifted from being a stealthy backdoor to a full-fledged proxy-building system. Today, attackers deploy it on compromised VPS servers to create large proxy networks. This development allows them to hide malicious traffic, making it harder for defenders to trace cyberattacks. How SystemBC Malware Operates

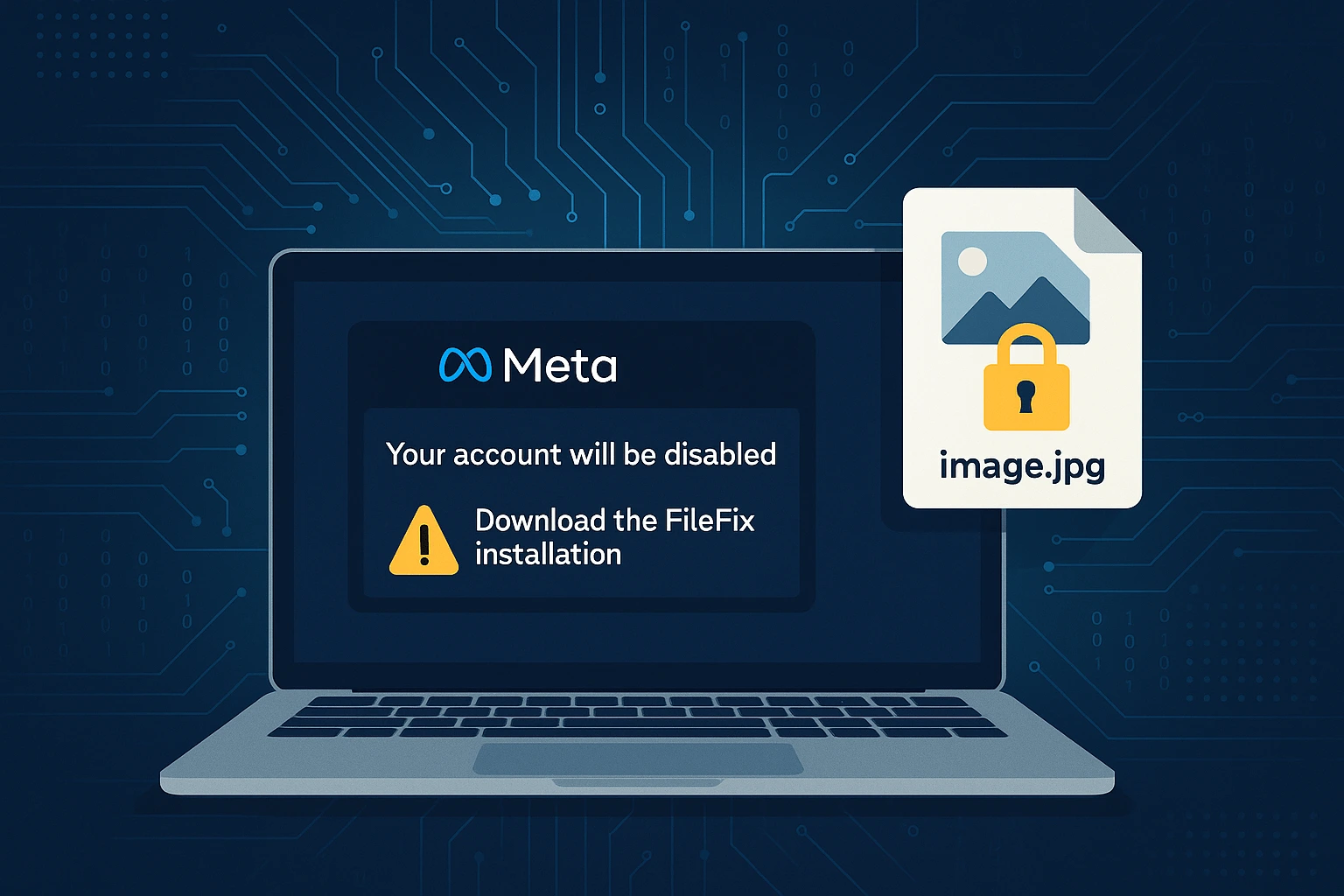
FileFix Attack Uses Steganography to Deliver StealC
A new FileFix attack campaign is targeting users with a blend of social engineering and advanced malware delivery. The operation impersonates Meta support notices to convince victims they must take action. Instead of fixing a problem, the tricked users end up executing hidden PowerShell commands. These commands launch a sophisticated chain of events that ends with the StealC infostealer installed
EggStreme Fileless Malware Targets Philippine Military
A newly identified threat named EggStreme fileless malware has been deployed by a suspected Chinese advanced persistent threat (APT) group. Researchers found the campaign targeting Philippine military systems, underlining the region’s rising geopolitical cyber risks. EggStreme stands out for its stealth. Instead of leaving files on disk, it executes in memory, making detection extremely difficult. This fileless design highlights the

AsyncRAT Exploits ConnectWise in New Malware Campaign
AsyncRAT exploits ConnectWise in a recent malware campaign that highlights how attackers weaponize legitimate remote access tools. Security researchers uncovered a layered attack chain that delivered the trojan through fileless techniques, persistence tricks, and data theft. The operation reveals the growing sophistication of remote access trojans and the increasing risks for businesses relying on widely used IT management software. How

Grok AI Exploit Spreads Malicious Links on X
Cybercriminals have uncovered a dangerous loophole in Grok AI, the chatbot integrated into X. By embedding harmful links inside video ad metadata, attackers trick the system into revealing them. This Grok AI exploit spreads malicious links to millions of users and raises major concerns about the safety of AI-powered assistants. How the Exploit Works The attack begins with a promoted

Claude AI Ransomware Abuse Sparks Cybersecurity Concerns
Claude AI ransomware abuse has raised new concerns about artificial intelligence in cybercrime. Recent reports show that threat actors are misusing Anthropic’s Claude models to create advanced ransomware campaigns. These cases highlight how AI can lower barriers for cybercriminals and accelerate the spread of Ransomware-as-a-Service. Cybercriminals Turn Claude Into a Weapon Investigators discovered that a threat actor identified as GTG-5004

Silk Typhoon Hackers Use Fake Portals in Espionage Campaigns
Silk Typhoon hackers hijack captive portals in diplomat attacks, exposing how far advanced persistent threats will go to steal intelligence. The group, also tracked as Mustang Panda, UNC6384, and TEMP.Hex, is a known Chinese state-sponsored operation. Their latest campaign reveals new tactics designed to bypass defenses and target high-value diplomatic missions. Hijacking Captive Portals Captive portals usually appear when users

ToxicPanda Android Malware Infects Thousands Across Europe
A new wave of the ToxicPanda Android malware is sweeping through Europe, targeting mobile banking users with advanced theft and evasion tactics. First identified in 2022, this banking trojan has evolved into one of the most dangerous threats for Android users, using fake overlays and accessibility services to steal login credentials and bypass security. Recent reports show over 4,500 devices

Lumma Infostealer Returns After Global Takedown
The Lumma infostealer malware has made a swift comeback after a coordinated takedown effort by global law enforcement agencies in May 2025. Despite the seizure of over 2,300 domains and major disruption to its infrastructure, the malware-as-a-service (MaaS) platform has bounced back with new distribution tactics and restored capabilities. Major Disruption, Minor Setback Lumma, also known as LummaC2, was targeted

Koske Linux Malware Hides in Panda Images to Evade Detection
A new Linux malware named Koske is using panda-themed image files to hide its malicious payloads. The threat actors behind it are leveraging polyglot files, legitimate JPEGs with hidden executable code. This stealthy malware targets poorly secured JupyterLab servers to gain access and then installs rootkits and cryptocurrency miners. Security researchers at Aqua Security discovered the campaign and say Koske