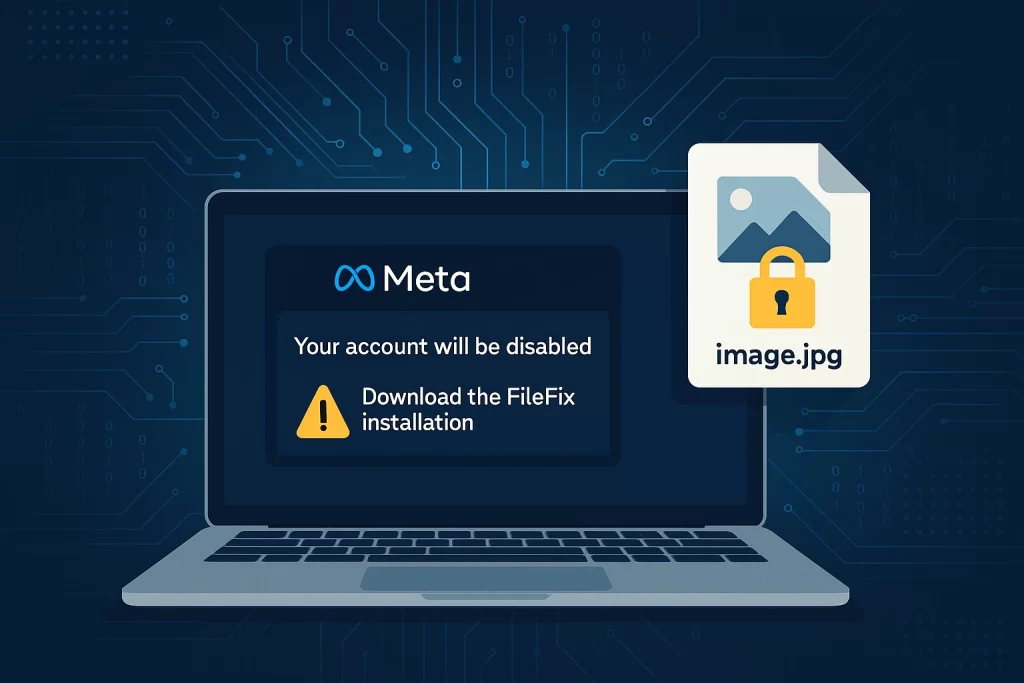
A new FileFix attack campaign is targeting users with a blend of social engineering and advanced malware delivery. The operation impersonates Meta support notices to convince victims they must take action. Instead of fixing a problem, the tricked users end up executing hidden PowerShell commands. These commands launch a sophisticated chain of events that ends with the StealC infostealer installed on the system. By combining familiar brand impersonation with steganography, attackers create a dangerous and convincing threat.
How the FileFix attack works
The FileFix attack is a variant of the earlier ClickFix technique. Attackers tell users to copy and paste text into the File Explorer address bar. The text looks like a safe file path but actually contains a hidden PowerShell command. Once executed, the command fetches a remote image that carries concealed malicious code.
By using added spaces and fake folder names, attackers disguise the payload as a harmless file location. This tactic lowers suspicion and helps the malware bypass casual inspection. Unlike older methods, FileFix avoids obvious markers, making detection harder.
Steganography inside image files
The campaign relies on steganography to hide its malware. Attackers host JPG images on platforms like Bitbucket. These images contain encrypted payloads embedded within the picture. When downloaded, a hidden script extracts and executes the malware directly in memory.
Because the malicious code never appears as a standard file, traditional antivirus tools may miss it. Steganography provides attackers with an effective way to bypass filters while appearing completely normal.
What StealC steals
The final stage of the attack installs the StealC infostealer. StealC is capable of stealing browser credentials, authentication cookies, and saved passwords. It also targets cryptocurrency wallets, cloud accounts, VPN logins, and even gaming profiles. In addition, the malware can capture screenshots and harvest a wide range of private data.
This makes StealC especially dangerous for both individuals and companies. A single slip can expose banking details, sensitive business information, or access to cloud platforms.
How to defend against FileFix attacks
Organizations should train employees not to paste commands from suspicious sources into system dialogs. Security teams should restrict PowerShell execution and log unusual command-line activity. Blocking downloads from untrusted hosting platforms reduces exposure.
Multi-factor authentication can limit damage if credentials are stolen. App allowlisting, browser hardening, and strong email filtering add additional layers of protection. From user awareness to endpoint controls, defenders must apply multiple safeguards.
Final Thoughts
The FileFix attack highlights the growing creativity of threat actors. By combining social engineering with steganography, attackers make malware campaigns harder to detect. Organizations and individuals must remain alert, train users, and enforce layered defenses. Vigilance and preparation are key to stopping StealC from spreading further.