Fog Ransomware Turns Legitimate Tools Against Defenders
In May 2025, incident responders at a regional bank in Southeast Asia stumbled upon a ransomware intrusion that looked nothing like the smash‑and‑grab playbooks they were used to. Instead of Cobalt Strike, MimiKatz or custom droppers, the adversary - operators of the Fog ransomware - stitched together a workbench of legitimate admin utilities and niche open‑source red‑team projects. Because every binary

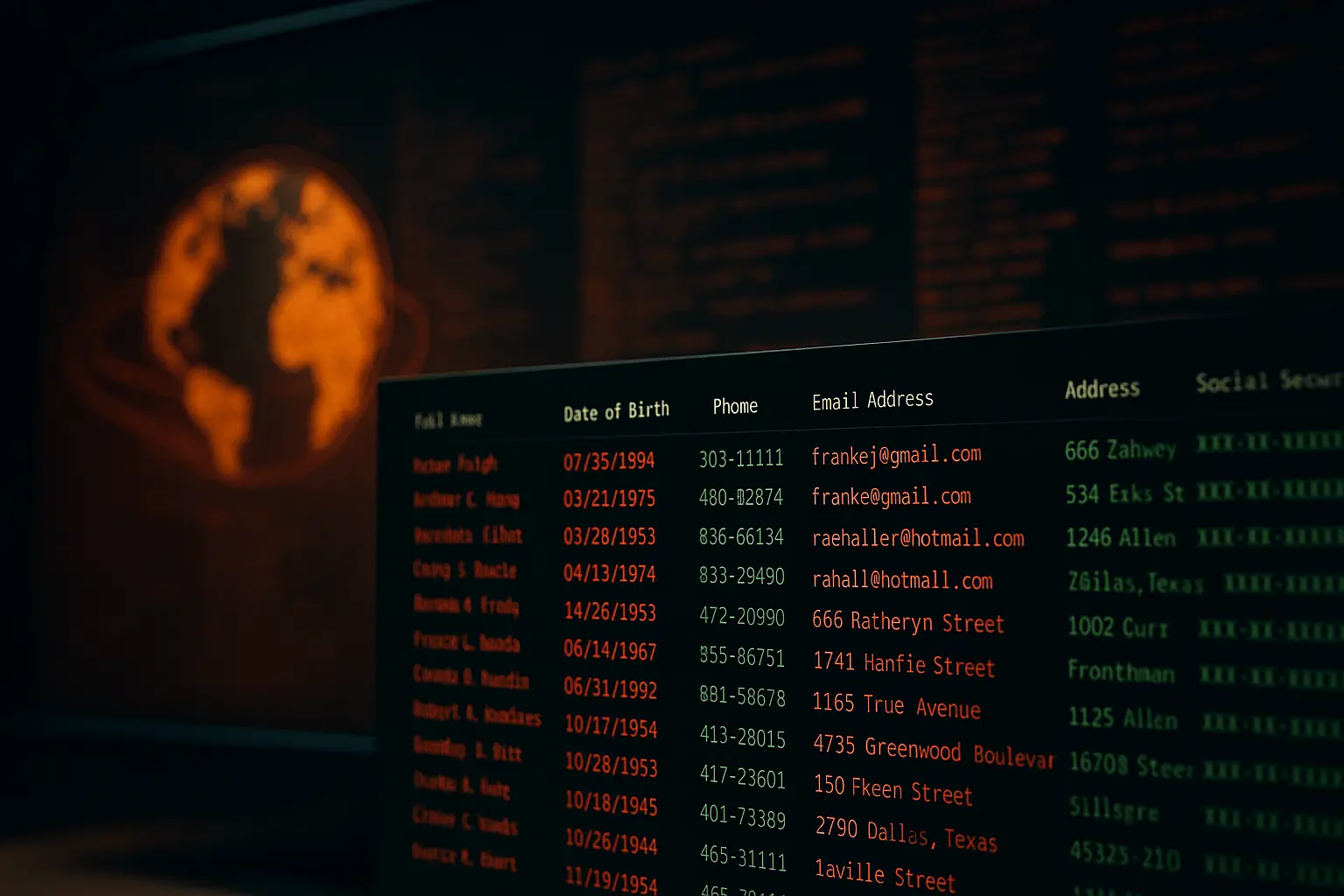
AT&T Data Breach Exposes 86 Million Records, Including SSNs
AT&T is under fire once again, but this time, it’s not just about poor service or billing issues – they suffered a data breach. In a deeply troubling turn of events, the personal data of approximately 86 million current and former customers has been leaked online, including an estimated 44 million Social Security Numbers (SSNs) in decrypted form. The breach
Play Ransomware Breaches 900 Victims Worldwide, FBI Confirms
The FBI, Cybersecurity and Infrastructure Security Agency (CISA), and Australian Cyber Security Centre (ACSC) have issued a joint advisory revealing that the Play ransomware group (also known as Playcrypt) has compromised over 900 organizations globally as of May 2025. This marks a sharp increase from the 300 known victims in October 2023, underscoring the escalating threat posed by the group.

Spear Phishing Campaign Targets CFOs and Abuses Legit Tools
A sophisticated spear phishing campaign that specifically targets CFOs (Chief Financial Officers) was recently uncovered by cybersecurity firm Trellix. This ongoing operation, first detected in mid-May 2025, has already affected organizations spanning Europe, Africa, Canada, the Middle East, and South Asia. The campaign’s method? A clever blend of social engineering and abuse of legitimate remote access software. Anatomy of the

Victoria’s Secret Cyberattack Shuts Down the Company Website
At the end of May 2025, Victoria’s Secret experienced a major cyberattack that forced the company to take its U.S. website offline. The sudden shutdown disrupted online shopping for millions of customers and caused ripple effects across its retail operations. Although the company has not shared specific details about the nature of the attack, the disruption suggests it may have

Dark Partners Cybercrime Gang Fuels AI and Crypto Heists
A new player has entered the cybercrime arena — and they’re not after just your passwords. The Dark Partners cybercrime gang is behind a sophisticated malware campaign that’s targeting users of AI tools, VPN services, and cryptocurrency platforms. By cloning popular websites like Windscribe, Ledger, and Sora, the gang lures victims into downloading malware disguised as legitimate software. The goal:

DragonForce Ransomware Hits MSPs via SimpleHelp
In a chilling reminder of the risks posed by insecure remote access tools, the ransomware group DragonForce has launched a sophisticated supply chain attack by exploiting critical vulnerabilities in SimpleHelp, a remote monitoring and management (RMM) platform widely used by Managed Service Providers (MSPs). The campaign, first uncovered by researchers at Group-IB, reveals how three recently discovered vulnerabilities in SimpleHelp

Coca Cola Data Breach Leaks Employee Info
In May 2025, Coca-Cola suffered a data breach - and not one, but two within days! These breaches exposed sensitive employee information and millions of internal Salesforce records, highlighting critical vulnerabilities in Coca-Cola’s security ecosystem. This incident serves as a stark reminder of the growing threat of sophisticated cybercriminals targeting multinational corporations. Everest Ransomware Targets Employee Information The first major

Operation Endgame: Europol Strikes a Blow to Ransomware
In a coordinated international crackdown, Europol, alongside law enforcement agencies from around the globe, has executed a sweeping operation that disrupted some of the world's most notorious ransomware operations. “Operation Endgame”, this large-scale effort resulted in the takedown of 300 servers, the neutralization of 650 domains, and the seizure of €3.5 million in cryptocurrency between May 19 and May 22,

Fake KeePass Version Executes Ransomware Attacks
A malicious version of the popular open-source password manager KeePass is being used to launch ransomware attacks on VMware ESXi servers. Security researchers have uncovered a trojanized variant, dubbed “KeeLoader” that mimics the real interface while silently compromising users' systems. Once installed, this fake KeePass plants a Cobalt Strike beacon and exfiltrates the user’s password database in plaintext. Thus, paving
