Instagram Data Leak Reports Dismissed by Meta
Claims of an Instagram data leak involving millions of user accounts spread quickly across hacking forums and social media. Posts advertising a dataset tied to roughly 17 million accounts raised immediate concerns about platform security and user privacy. The allegations triggered a rapid response from Instagram and its parent company Meta, which both denied that a breach had occurred. According

BreachForums database leak exposes 324,000 forum accounts
A major BreachForums database leak has exposed account data linked to roughly 324,000 users of the well-known hacking forum. The leaked dataset surfaced online after unknown parties gained access to the forum’s user database and published it publicly. Although the exposure does not include plaintext passwords, the incident still presents serious risks for users who relied on anonymity. The leak

European Space Agency Breach Linked to External Servers
A confirmed European Space Agency breach has drawn attention to the growing security risks tied to external digital infrastructure used by major institutions. The incident involved servers that support collaboration with external partners rather than core mission systems, yet the scope of the exposure has raised serious concerns across the cybersecurity community. The case highlights how attackers increasingly target secondary

Korean Air Data Breach Exposes Employee Information
A significant security incident has affected one of Asia’s largest airlines after Korean Air data breach disclosures confirmed unauthorized access to employee systems. The breach exposed personal information belonging to thousands of current and former staff members and remained undetected for several months. The incident did not disrupt flights or customer-facing services. However, it revealed serious weaknesses in how internal

Nissan Confirms Customer Data Exposure After Red Hat Breach
Nissan has confirmed a Nissan customer data exposure after attackers gained unauthorized access to a Red Hat–hosted development environment. The incident did not impact Nissan’s production systems, yet it still exposed sensitive customer information stored in a third-party cloud setup. The case highlights how non-production environments remain an attractive target for attackers seeking valuable data with fewer defenses. What happened

Askul Data Breach Confirms 740,000 Records Stolen
The Askul data breach has confirmed a significant ransomware incident involving one of Japan’s largest office supply and e-commerce companies. After weeks of investigation, Askul revealed that attackers stole roughly 740,000 customer records during a cyberattack that disrupted internal systems and logistics operations. What initially appeared to be a technical failure later proved to be a coordinated ransomware intrusion linked

700Credit Data Breach Exposes 58 Million Dealership Customers
A large-scale 700Credit data breach has quietly exposed sensitive personal information linked to tens of millions of vehicle dealership customers in the United States. While the incident did not originate inside dealership networks, it still carries serious consequences for consumers whose data passed through a trusted third-party platform. The breach highlights a familiar but persistent problem. As businesses outsource critical

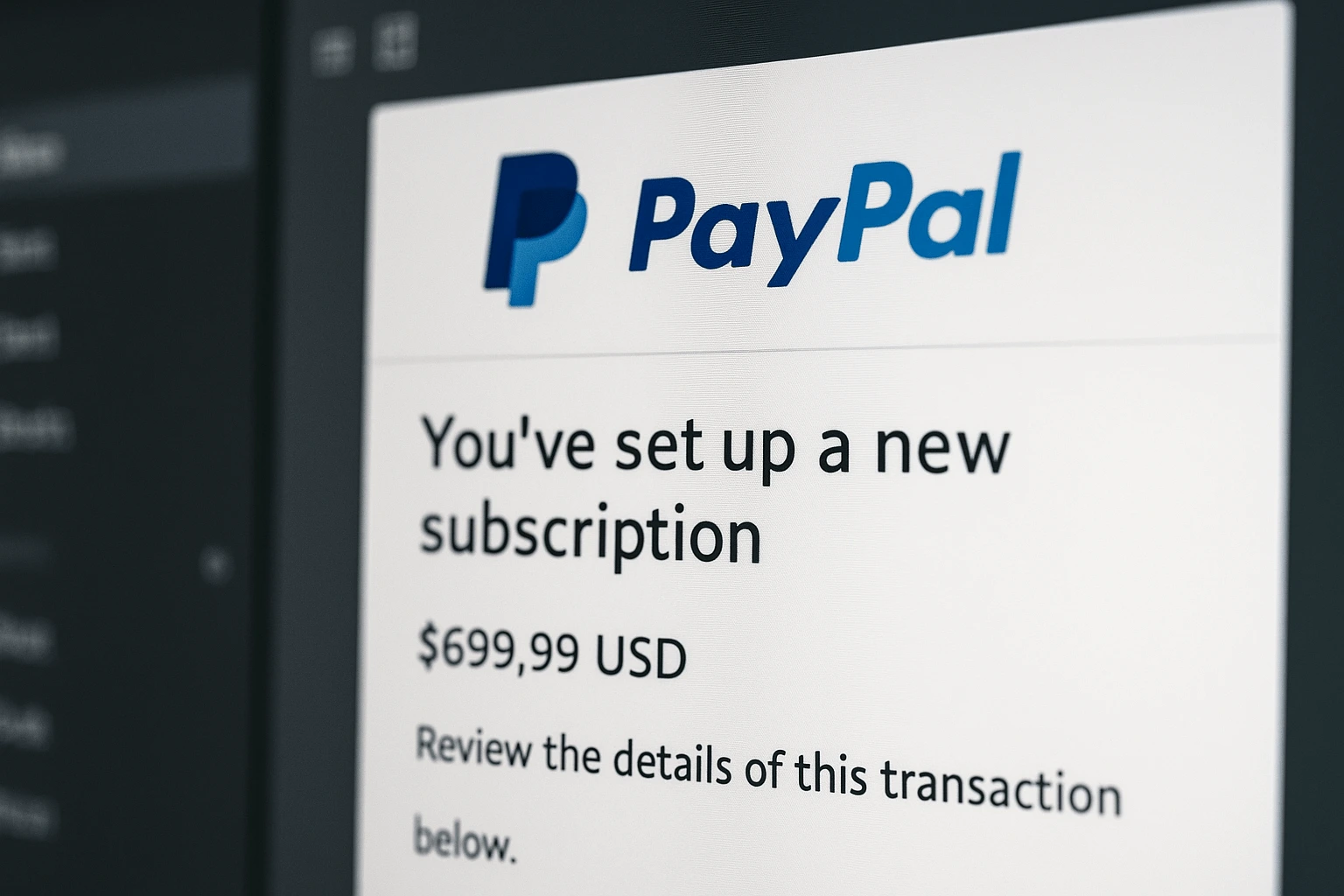
PayPal Subscription Scam Abuses Legitimate Billing Emails
A PayPal subscription scam is circulating that does not rely on fake domains, malicious links, or compromised accounts. Instead, it abuses a legitimate PayPal feature to deliver fraudulent messages directly from PayPal’s own email infrastructure. The result is a scam that bypasses many traditional warning signs and places users at risk through trust rather than technical deception. Security researchers warn
Coupang Data Breach Traced to Former Employee Access
The Coupang data breach did not follow the familiar pattern of modern cyber incidents. There was no ransomware deployment, no phishing campaign, and no external attacker exploiting a technical vulnerability. Instead, the exposure originated inside the company, where a former employee retained access to internal systems after leaving their role. For Coupang, one of South Korea’s largest e-commerce platforms, the

Inotiv Cyberattack Exposes Data after Confirmed Network Intrusion
Inotiv, a US-based contract research organization supporting pharmaceutical development, has confirmed a serious cyber incident. The Inotiv cyberattack involved unauthorized access to internal systems and confirmed data theft. The disclosure adds to growing concerns about ransomware activity targeting healthcare and life sciences companies. What Happened During the Inotiv Cyberattack Inotiv detected the intrusion in early August after attackers gained access
