ChatGPT Search Update Challenges Google
The latest ChatGPT Search update marks a major leap in OpenAI’s efforts to compete with Google. The improvements focus on accuracy, usability, and intent recognition, aiming to provide users with faster, smarter, and more reliable search results. By refining how the system processes and delivers information, OpenAI positions ChatGPT as a direct rival to traditional search engines. Smarter Search Results

RaccoonO365 Phishing Service Disrupted by Microsoft and Cloudflare
Microsoft and Cloudflare have joined forces to dismantle the RaccoonO365 phishing service, one of the most widespread phishing-as-a-service operations uncovered to date. The joint takedown targeted the infrastructure and domains used by cybercriminals to conduct massive credential theft campaigns against Microsoft 365 users worldwide. This disruption represents more than just the removal of malicious domains. It highlights the ongoing battle

SystemBC Malware Turns VPS Into Proxy Networks
SystemBC malware is evolving into a powerful tool for cybercriminals. First spotted in 2019, it has shifted from being a stealthy backdoor to a full-fledged proxy-building system. Today, attackers deploy it on compromised VPS servers to create large proxy networks. This development allows them to hide malicious traffic, making it harder for defenders to trace cyberattacks. How SystemBC Malware Operates

SonicWall MySonicWall Breach Forces Credential Resets
The SonicWall MySonicWall breach has prompted urgent warnings from the cybersecurity vendor. SonicWall advised all customers to reset credentials and enable multi-factor authentication after attackers gained access to customer accounts. The incident highlights the growing risks tied to vendor platforms that hold sensitive client data. Breach Overview SonicWall confirmed unauthorized activity within its MySonicWall customer portal. This platform manages product

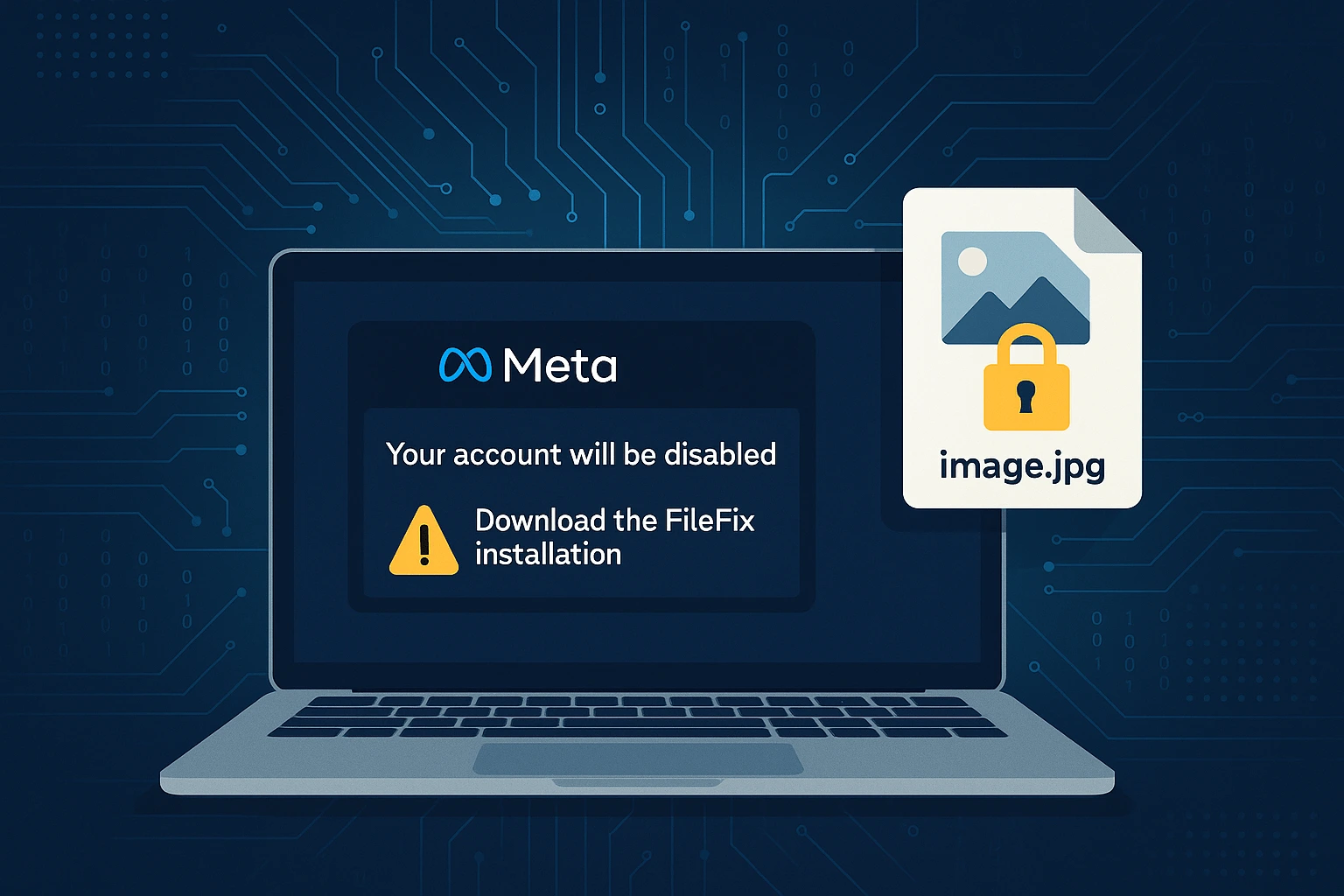
FileFix Attack Uses Steganography to Deliver StealC
A new FileFix attack campaign is targeting users with a blend of social engineering and advanced malware delivery. The operation impersonates Meta support notices to convince victims they must take action. Instead of fixing a problem, the tricked users end up executing hidden PowerShell commands. These commands launch a sophisticated chain of events that ends with the StealC infostealer installed
GPT-5 Codex Model Challenges Claude Code in AI Programming
OpenAI has released the GPT-5 Codex model, a significant update designed to transform AI-assisted programming. This version challenges Claude Code, Anthropic’s coding solution, by delivering measurable performance gains. Developers can expect greater precision, more efficient refactoring, and improved reliability across coding tasks. The update reflects OpenAI’s push to strengthen its leadership in AI-driven development. What Makes GPT-5 Codex Different It

VoidProxy Phishing Targets Microsoft 365 & Google Accounts
The VoidProxy phishing attack is an emerging cyber threat targeting cloud accounts on Microsoft 365 and Google platforms. This attack service enables attackers to bypass multi-factor authentication (MFA) and steal sensitive credentials. VoidProxy is designed for simplicity, allowing low-skill cybercriminals to deploy phishing campaigns with minimal effort. As organizations increasingly rely on cloud services, understanding this threat and implementing preventive

Jaguar Land Rover Data Breach Confirmed After Cyberattack
The Jaguar Land Rover data breach reveals the growing cybersecurity threats facing global automakers. The company confirmed that a recent cyberattack not only disrupted manufacturing but also compromised data. While the full scope remains unclear, the breach highlights the vulnerability of complex supply chains and the need for stronger digital defenses across the automotive sector. Cyberattack Causes Factory Shutdowns The

Akira Ransomware SonicWall Bug Exploited Despite Patches
The Akira ransomware SonicWall bug exploitation highlights the ongoing danger of incomplete patching in cybersecurity. Attackers are actively abusing the critical flaw CVE-2024-40766, first disclosed in August 2024. While SonicWall released fixes over a year ago, many organizations remain exposed due to overlooked remediation steps, leaving them vulnerable to fresh ransomware campaigns. The Flaw Behind the Attacks CVE-2024-40766 is a

EggStreme Fileless Malware Targets Philippine Military
A newly identified threat named EggStreme fileless malware has been deployed by a suspected Chinese advanced persistent threat (APT) group. Researchers found the campaign targeting Philippine military systems, underlining the region’s rising geopolitical cyber risks. EggStreme stands out for its stealth. Instead of leaving files on disk, it executes in memory, making detection extremely difficult. This fileless design highlights the
