Fake system crashes have become a powerful tool for modern malware campaigns. Instead of exploiting software flaws, attackers increasingly rely on fear and urgency to push users into dangerous actions. One of the clearest examples of this shift is the ClickFix BSOD attack, which uses convincing Windows Blue Screen of Death visuals to manipulate victims into executing malicious commands themselves.
By imitating a critical system failure, attackers bypass traditional security barriers without triggering exploit-based defenses. The technique works because users trust familiar Windows error screens and act quickly when they believe their system is at risk. This makes the attack effective even in environments with strong technical protections in place.
How the Attack Begins
The attack typically starts when a victim visits a malicious or compromised website. This can happen through malvertising, phishing messages, or manipulated search results that lead to attacker-controlled pages. Once the page loads, embedded scripts immediately take over the browser window and display a full-screen fake system crash.
The site disables common browser interactions, such as right-clicking or closing the tab normally. This restriction reinforces the illusion that the operating system has crashed, not just the browser. As panic sets in, users focus on the message in front of them instead of questioning its legitimacy.
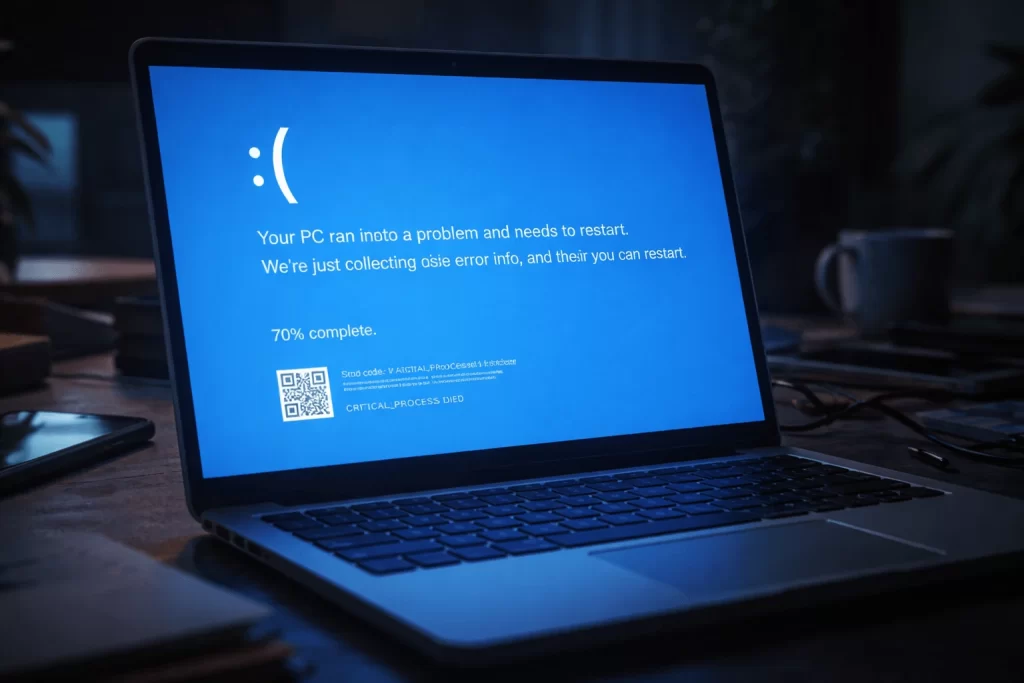
Fake BSOD Screens Create Urgency
The fake crash screen closely imitates a real Windows BSOD. It uses familiar colors, formatting, and technical language that appears authentic at first glance. Some versions include fake stop codes or claim that critical system files have failed, which adds credibility for less technical users.
Instead of suggesting a reboot, the screen presents instructions that promise an immediate fix. This shift matters because it keeps users engaged and pushes them toward action rather than reflection. By the time doubt arises, the attacker has already moved the victim closer to executing malicious commands.
Social Engineering Replaces Exploits
At the core of the ClickFix technique is social engineering. The fake BSOD instructs users to open the Windows Run dialog and paste a command that is supposedly required to repair the system. These steps look harmless and even routine, especially to users familiar with basic troubleshooting.
The crucial detail is that the attacker never executes malware directly. The victim does it voluntarily, believing they are resolving a system failure. This design allows the attack to bypass many security warnings and exploit protections that focus on automated or unauthorized execution.
Clipboard Manipulation Enables Execution
The malicious page silently places a command into the user’s clipboard. When the victim pastes it into the Run dialog, they unknowingly trigger a process that downloads and launches malware. This technique removes the need for visible downloads or suspicious prompts that might raise alarms.
Attackers typically rely on trusted Windows utilities to perform these actions. Because the commands originate from legitimate system tools and appear user-initiated, many endpoint protections treat the behavior as normal.
Malware Delivery and Payload Flexibility
Once executed, the command retrieves a payload from a remote server and runs it immediately. The malware may save itself in temporary or user-accessible directories before launching additional components. PowerShell commands often hide execution windows and bypass basic policy restrictions to avoid user suspicion.
The ClickFix method supports a wide range of payloads. Campaigns have delivered information stealers, remote access trojans, and loader malware designed to fetch additional tools later. This flexibility allows attackers to reuse the same delivery framework for different objectives, from credential theft to long-term access.
Post-Infection Activity and Persistence
After infection, the malware may establish persistence through registry entries or scheduled tasks. It can collect browser data, credentials, and system information before communicating with command-and-control servers. In some cases, secondary payloads follow once the attacker confirms successful installation.
Because the user initiated the execution, incident timelines often appear less suspicious at first glance. This delay can give attackers more time to operate before detection and response efforts begin.
Why the Attack Works
The effectiveness of the ClickFix BSOD attack comes from its reliance on human behavior. It avoids exploits entirely, uses familiar system visuals, and leverages trusted tools that security software rarely blocks outright. Even cautious users can make mistakes when faced with what looks like a system-level failure.
This approach highlights a growing trend in malware campaigns that focus on manipulating users instead of bypassing technology.
Defensive Challenges and Mitigation
Defending against this technique requires more than signature-based detection. Organizations need visibility into command execution, script usage, and unusual PowerShell behavior. Restricting script execution and monitoring clipboard abuse can also reduce exposure.
User awareness plays a critical role. Teaching users that legitimate system crashes never instruct them to paste commands from websites can stop these attacks before they succeed.
Final Thoughts
The ClickFix BSOD attack demonstrates how effective social engineering has become in modern malware campaigns. By imitating trusted system errors and shifting execution to the victim, attackers bypass many technical safeguards without exploiting a single vulnerability.
As defensive tools continue to evolve, attackers will keep targeting the most unpredictable element in any environment.